Protect Yourself From Future Phishing Scams
Information and Technology Services (ITS) was alerted to the phishing scam and blocked access to the malicious website designed to compromise your personal information. The link now points to this page, intended to help you better identify and protect yourself from future phishing scams.
What is Phishing
Phishing is the attempt to obtain sensitive information such as usernames, passwords, social security numbers, and financial information, often for malicious reasons. By leveraging public information, such as email addresses from the University Phonebook, these message can appear legitimate.
Although the University’s spam mail filters and security processes reduce the threat to our community, they cannot eradicate all phishing. The best way to avoid being a victim of a phishing scam is to not fall for it.
How to Detect and Handle Phishing Messages
Step 1: Identify the message as a phishing scam.
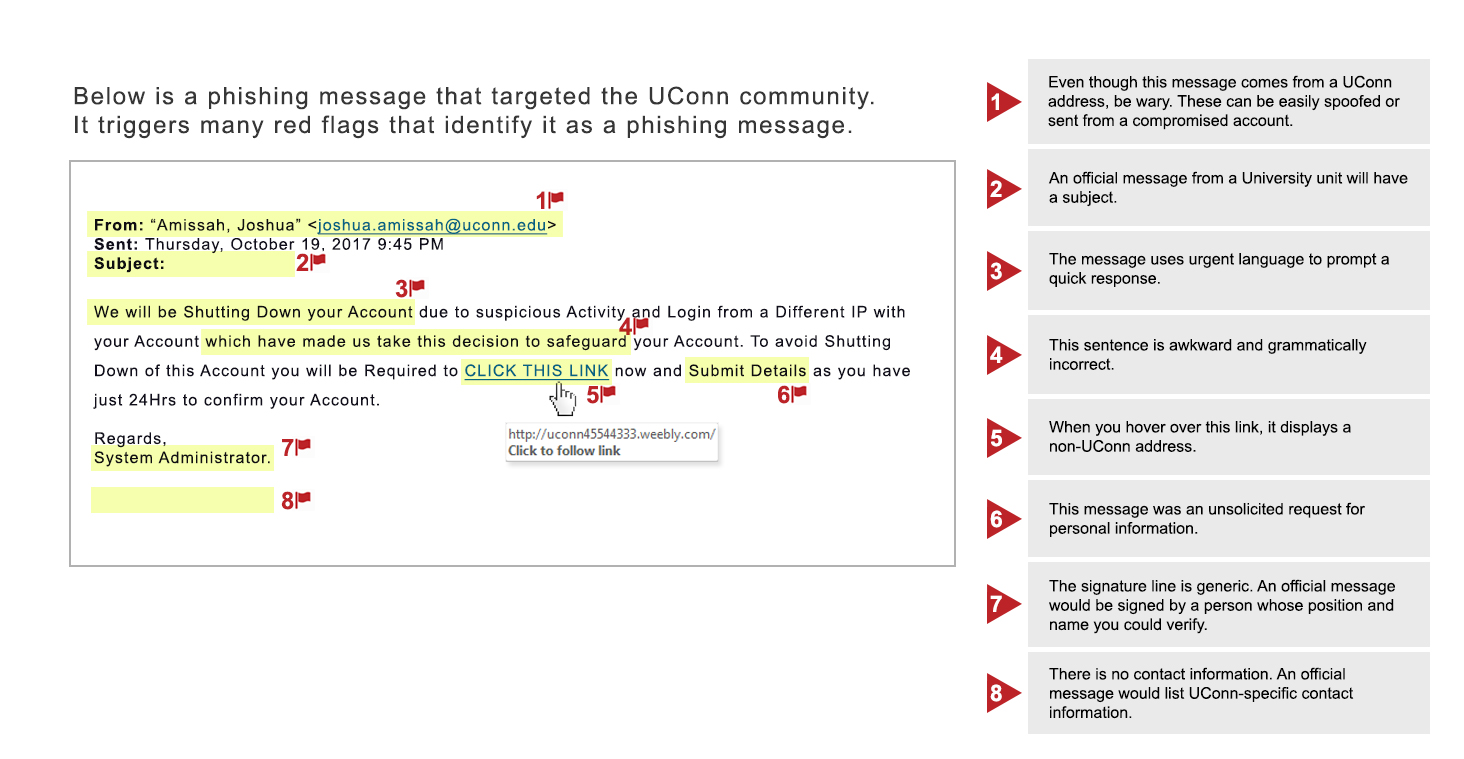
Some red flags include:
- Urgent requests. Phishing attacks attempt to induce panic in the receiver and cause the person to act before investigating the authenticity of the request.
- Bad spelling or grammar. Phishing messages are notorious for containing misspelled words, awkward phrasing, or poor grammar.
- Attachments. Phishing messages may attach fake documents or files to trick you into opening up malware installments.
- Mismatched email address information. Make sure the email address displayed in the From: field matches address listed in behind mailto:.
- Requests to click a link. Attackers commonly use links to redirect you to unsecure websites or pages spoofing official organizations.
- Generic signature line. Authentic messages are typically signed by official contacts or names, while phishing messages may be signed by generic company names or roles.
- Offers that are too good to be true. Phishing attacks can play on your emotions and offer false hope in the exchange for your personal information in the form of job offers, acceptance messages, or “congratulations, you won!” scams.
- "Message sent from a System Outside of UConn." If an email appears with a banner stating it was sent from outside of UConn, then it is not an official university message.
- Unexpected requests regarding personal information. Be extremely wary of following links or answering questions from contacts you did not initiate.
Step 2: Check out links and attachments before you click.
- Links can direct you to spoofed web pages or download harmful files on your system. You can hover the cursor over the link before you click on it to ensure that the address matches the link that was typed. You can always check the legitimacy of a message by going directly to the company or organization website or contacting them via phone.
- Hover over an attachment to verify that the title matches the file type. A document that looks like it has a name “something.pdf” might actually be a file “something.exe.” An .exe extension means the attachment is actually a software program that you execute and is extremely dangerous; it can cause computer infection and data loss.
Step 3: Report and delete
If you suspect that the email is a phishing message, forward it to reportphishing@uconn.edu. Then delete the message from your inbox.
Security Service Update
UConn has enabled Advance Threat Protection (ATP) on all University email services. ATP provides protection against malicious links and unsafe attachments.
- Links: All URLs are rewritten through Microsoft 365. If a link is safe, you will still go to the intended location. If a link is unsafe, you will see a warning message.
- Attachments: All attachments are scanned for malware and access to attachments considered unsafe will be blocked.
Before implementing this service, ITS would advise you to hover over links and attachments and ensure that the link and address matched. With this service, all links are rewritten in Microsoft 365 and will not match the URL displayed in the message.
ATP provides you with additional protection from unsafe links and attachments. However, continue to exercise caution and do not click on suspicious links. No detection method can provide complete protection.
What to Do if You Click on the Links in a Phishing Message
- Change your NetID password immediately.
- Contact the ITS Tech Support Center at 860.486.4357, techsupport@uconn.edu, or via the online chat at techsupport.uconn.edu.